Trusted Professionals
Your work is trusted, are your records?
How much would it cost to defend yourself?
Records Integrity is Critical
If your work is ever wrongfully challenged, your records will be your best tool to vindicate yourself. e-TimeStamp trusted timestamps are a gold standard in demonstrating records-integrity thanks to rigorous implementation of international standards.
You can use us for CPA Audit Documentation (SAS 103).
We aid in compliance with HIPAA, SOX, and CFR 11.
Why use e-TimeStamp?
- Prove your data existed in its unaltered state, then and now
- Bind your name to your work to add evidence that its content originated with you
- Possess strong legal evidence backed by international standards
- Integrate our software into your existing software tools
- Provides a viable, low-cost solution to data integrity in electronic workflow
How it works
|
First, a digital fingerprint of your file is generated on your computer. |
See how easy it is to get protection! |
|
Next, this digital fingerprint is sent to a DigiStamp Timestamp Authority. |
The Timestamp Authority creates a timestamp with the fingerprint, the authority's digital signature, and the current time.
The timestamp is returned to you as a certificate, for your safe keeping, verifying the file's existence at the moment of timestamping. This certificate is proof that the file has not changed since being protected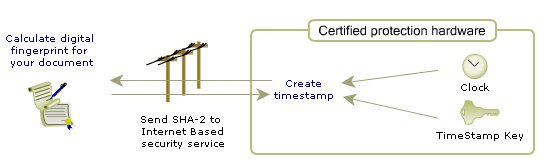
Important Considerations:
- You should include your name in the file that you timestamp, otherwise all that will be proven is that the file existed at a point-in-time.
- You must retain a copy of the file version you timestamped. A modified version will no longer have the same digital fingerprint so it will not be protected.
- You must retain a copy of the timestamp certificate to protect the authenticity of your records.
What you'll need to do
Protecting your records has never been this cheap or this easy:
First, you'll need to have a digital file of your records. If your records were not created digitally, this can be a scan, recording, or any other digital file that represents the work you need to protect.
Next, you'll need to make an account with DigiStamp. There is a minimum charge of $10 to use the service, but timestamps cost only $.40. Ten dollars allows you to protect 25 records.
Now, you're ready to make your first e-Timestamp with our web applications, or other programs like Adobe Acrobat or Microsoft Office.
Video demonstrations of how to use our web applications and the IP Protector are available.
Add Inexpensive Third Party Witness to your Records:
Does an e-TimeStamp meet the legal standard for using electronic records as legal evidence?
The digital timestamp was defined by open standards as part of the technology called Digital Signatures, or PKI. DigiStamp uses this accepted method and then adds an external audit and certified hardware to provide a trusted web-based service. The result is strong evidence to prove that your computer files are authentic.
In general, electronic records are legally admissible in the United States if they can be reliably shown to originate with systems that provide accurate results. The accuracy of our records is supported by the code signing event and HSM birth ceremony which every timestamp can be traced back to, and which exist in public record due to the testimony of auditors. The code signing event, when the code used in every SecureTime HSM was locked down with multiple digital signatures, included a thorough review of our source code by 2 auditors. Their testimony indicates that our code correctly implements RFC 3161, an IETF standard for the evidence we create.
In the United States, "E-SIGN" is a federal law that gives electronic signatures, contracts and records the same validity as their handwritten and hard copy counterparts. (The Electronic Signatures in Global and National Commerce Act, 2000). The ESIGN law provides guidelines to eliminate legal barriers to using electronic signatures for signing contracts and storing documents. The law promotes uniformity in electronic contracting nationwide by pre-empting inconsistent state laws. Many of those laws are derived from the Uniform Electronic Transactions Act ("UETA"). The DigiStamp services are consistent with these guidelines. More information on E-Sign is here.
Company compliance with government and industry regulations - DigiStamp operates with compliance to e-signature practices set forth in 21 FDA CFR-11 and regional requirements like eIDAS (Electronic Identification and trust services). DigiStamp acting as a trust service provider, we produce electronic time stamps through use of advanced electronic seals. The medical industry is focused on two sets of regulations called HIPAA, FDA CFR-11 and GxP. Details here
Additional laws define the legal environment for DigiStamp services:
18 U.S.C. 1343 Wire Fraud
18 U.S.C. 2701 Electronic Communications Privacy Act (ECPA)
18 U.S.C. 2510 regarding electronic communications
18 U.S.C. 1028, Fraud and related activity in connection with identification documents and information
We suggest that you discuss with your attorney the specifics of your situation and we publish a legal counsel disclaimer here.
Consider that large corporations have used this technique for years as part of their proof of intellectual property rights. Now, due to the Internet technologies, this service is more universally available.
Comply with HIPAA, SOX, and CFR-11
Has a timestamp been used to settle a legal dispute?
DigiStamp has created more than 1 million timestamps for customers and none have been challenged in court. Our service creates strong legal evidence by using an external audit and certified hardware.
In existing case law, digital evidence of a lower quality than DigiStamp's has been accepted; provided proper protocols were followed. DigiStamp uses automated and aggressively defensive modules to encapsulate the creation of evidence, so that it is nearly impossible for protocol to be disrupted. Furthermore, verification can be performed immediately.
It is important to note that an estimated 95% of legal evidence is challenged in early stage discovery, not in court. While DigiStamp can add legal strength to a court case, the third-party timestamp provides evidence to help resolve or avoid disputes prior to courtroom litigation. The legal community has described the situation where the timestamp or digital signature is presented as evidence between opposing parties before presenting their cases. The opposing counsels chose not to spend the effort to attempt to refute the timestamps, so this one point was just accepted. Therefore, this form of evidence did not convert to case law because it was not refuted in the courts.
See related subjects of legal standards and the DigiStamp external audit and certified hardware.
What if DigiStamp ceases to offer their timestamp service or goes out of business?
You can verify a timestamp without contacting DigiStamp - you do not depend upon DigiStamp offering this service or being in business. A timestamp from DigiStamp has no defined expiration, and can be renewed later by DigiStamp or another party.
Our timestamps are provided as an industry-standard 'digital signature' record. Therefore, other software can be used to verify a timestamp from DigiStamp. You would need:
- Your original, unchanged file
- The timestamp you created using DigiStamp's service
- Our public key, an x.509 public key certificate (included as part of the timestamp)
A copy of the public key certificate is transferred to your computer inside the timestamp, when you create your timestamp. The certificates can be retrieved manually from the DigiStamp web site here.
If we went out of business we would publish all of our audit documents, which could be compared directly to the timestamps you receive. Your timestamps could be traced all the way back to the two audited events for the TSA which created it.
Details on how to verify a DigiStamp e-TimeStamp are available here.
Why do I keep my own timestamps instead of DigiStamp?
An e-TimeStamp is independently verifiable proof which conforms to numerous international standards.
DigiStamp recommends you store the timestamp next to the original file (or an archive copy) since both must be maintained to protect your transaction. The timestamp returned is less than 3000 bytes and includes all the data needed to verify it using standard methods. If your application requires DigiStamp retain your timestamps, please contact DigiStamp with your requirements.
How tamper-proof are the timestamps ?
The timestamps cannot be forged by anyone, including the people at DigiStamp. DigiStamp uses both one-way hashing and very strong encryption to ensure the integrity of its timestamps. A "one-way hash function" yields a hash value or fingerprint of the file from which it is impossible to reproduce the original file. It is "one way" because one can go from the file to the hash value, but one cannot reproduce the file from the hash value. If even one bit is changed or moved in the original document, then the hash value would also change. But, if the same hash function is applied to the same original file, the same hash value is always generated. Thus applying the same hash function to the original file and comparing that with the timestamp content will reveal whether the file has been altered.
An originator transmits a representation of a digital file, its hash value, to DigiStamp for timestamping. DigiStamp creates a timestamp containing the hash value of the file and the current time and then applies its verifiable digital cryptographic signature. The strength of a cryptographic signature depends on the key size of the algorithm used. RSA 2048-bit key asymmetric encryption is used, one of the strongest on the market.
What industry standards are supported?
The primary source for standards we use to manage and create the timestamp service are defined by the Internet Engineering Task Force (IETF). The timestamp is an extension to the Public Key Infrastructure (PKI) used for digital signatures. This industry-standards body meets regularly to advance the Internet and its ubiquitous uses. Its proceedings and standards can be found at the IETF web site. A few of the core message-format supports are as follows. A more extensive list in on Page 5 of DigiStamp's TSA Policy and Disclosure.
Signed Content - The signed message contains the time from DigiStamp's secure clock and the message digest of your document as defined in the timestamp x.509 PKI Timestamp Protocol IETF RFC 3161 and the update RFC 5816. This standard was later described in standards ISO/IEC 18014-2, ETSI TS 101 861, and ANSI X9.95
Evidence Records - Processing rules and an XML format for maintaining and communicating long-term records of the existence and integrity of data, IETF RFC 6283. This is an XML Syntax (XMLERS) version of the prior ASN.1 version described in RFC 4998.
Timestamp Token - The timestamp service returns a signed message in the standard form of Cryptographic Message Syntax, based on PKCS #7 version 1.5, IETF RFC 2630.
Company operations and policy - These policy requirements are aimed at timestamping services used in support of qualified electronic signatures. This standard may be used by independent bodies as the basis for confirming that a TSA may be trusted for providing timestamping services. Users can consult the DigiStamp's practice statement to obtain further details of precisely how this timestamp policy is implemented. The standard is published as: Policy Requirements for Timestamping Authorities IETF RFC 3628 and is technically equivalent to ETSI TS 102 023.
Company compliance with government and industry regulations - DigiStamp operates with compliance to e-signature practices set forth in 21 FDA CFR-11 and regional requirements like eIDAS (Electronic Identification and trust services). DigiStamp acting as a trust service provider, we produce electronic time stamps through use of advanced electronic seals. The medical industry is focused on two sets of regulations called HIPAA, FDA CFR-11 and GxP. Details here
Public Keys - The public portion of the signing key is available as an x.509 certificate IETF RFC 2459
Message Digest - A unique value is calculated from the data to be timestamped using the SHA-2 message digest as defined in the Federal Information Processing Standard Publication 180-4 "Secure Hash Standard". The variety of hash algorithms we support is here.
Long-term, legally-binding digital signatures - A common use-case creating a timestamp of a digital signature. This enable rely parties to prove that the digital signature from the signer was applied when the signer's certificate was valid. The process is defined the digital signature standards IETF RFC 5126 "CMS Advanced Electronic Signatures (CAdES)" and the equivalent European digital signature standard ETSI 101 733 V.1.7.4
Why you can trust it
DigiStamp provides strong legal evidence for authentication
Simply put, you need proof of what you've done and when you did it. Our service provides strong evidence for both.
In fact, we provide uniquely strong evidence, in part because we have implemented internationally standardized methods.
No one can use our service to produce a false timestamp. Even we can't produce false timestamps. If someone offered us a million dollars, we still couldn't produce a false timestamp.
Why not? A DigiStamp timestamp offers you three layers of security:
- An audit trail from two independent authorities proving that our equipment does exactly what we say it does.
- State-of-the-art software that meets the highest established standards.
- Uniquely customized hardware that cannot be tampered with.
Details on this security are available here.Details on why our product works are available here.
Our timestamps have not been successfully challenged in 10 years of operation. Many organizations have trusted us to protect intellectual property and records of great value to their operations.